Web DRM, an Overview (1) - Digital Content Protection
Protecting copyrighted content has always been a priority for many businesses, from the past to the present. In the digital era, this task has become more challenging due to the ease of copying content. Modern enterprises now rely on a range of strategies to prevent piracy.
Due to the open nature of the internet era, browsers cannot prevent users from accessing the source code. This makes protecting intellectual property on websites quite challenging. This article specifically introduces digital content protection strategies in the Internet age.
What is DRM?
For protecting digital intellectual property, the most common method is DRM (Digital Rights Management). In simple terms, it manages how and whether consumers can "copy" digital assets. People who are familiar with gaming will recognize DRM, as many modern games use it to prevent copying and require identity verification for play.
Early DRM mainly used streaming and real-time decryption, especially in DVDs. This involved encrypting DVD content, which was then decrypted in real-time by authorized devices during playback. In recent years, large games often use tamper-proof mechanisms, wrapping the game program in a layer that decrypts command codes in real-time, which can significantly reduce performance.
Since DVDs are usually decrypted quickly by hardware, this wasn't a big issue. However, in modern 3D games where CPU resources are maximized, DRM's impact on performance often draws complaints from players. This is why DRM is notorious in the gaming world.

Various Forms of DRM
DRM isn't just real-time decryption. Practically, any technology that prevents the abuse of intellectual property is considered DRM. For example, some games don't use real-time decryption but require a constant internet connection to verify the player's identity.
Other common methods include:
Serial number authentication.
Connecting to a server for membership registration and identity verification.
Server control over the number of devices a software can be installed on.
Limiting the number of copies or downloads.
Hardware to anti skimming or recording.
Using specialized devices to view/access resources.
Watermarks (yes, just a simple tracking of leaking data also considered as a DRM).
Metadata (declaring copyright in the metadata of files or photos).
Monitoring users' behavior and reporting to the backend.
Detecting if software or resource content has been tampered with, and stopping operation if so.
Using a central marketplace to sell resources and centrally verify identities (similar to the Apple App Store or Steam).
Requiring an online download after purchase.
There are many methods, some even raising privacy concerns. However, due to commercial interests, many manufacturers still opt for these protection mechanisms.
How is Website DRM Implemented?
Let's talk about DRM on websites, which commonly protects audio-visual content, ebooks, software, or resource materials. However, implementing DRM on websites is generally ineffective.
Why is Website DRM Considered Ineffective?
The reason is that web browsers are open environments. The JavaScript code isn't compiled, so anyone can see the source code. In such an environment, any encryption program, if executed on the browser side, can be easily cracked.
Moreover, all content viewed in a browser—audio, video, images, text—must be downloaded to memory to display, and browsers easily allow users to open and save these resources.

This image shows how easy it is to capture a video's original file from a website using a browser.
Due to this openness, any encryption can't prevent the final action of saving files from the record, making it pointless to encrypt resources.
What Other Methods Exist for Web DRM?
As mentioned before, DRM isn't just about encryption. Any method that can prevent copying or make stealing more difficult is considered DRM. Here are some common DRM methods used online, none perfect, but they make illegal copying harder.
For Graphic and Text Resources
Locking right-click to block copying.
Converting text into images.
Verifying member identity for access.
Server outputs a small chunk of graphics and text at a time, with identity verification for each access.
Using specialized devices or software to view graphics and text.
Embedding watermarks in images.
Automatically adding copyright statements when copying text.
For Downloadable Resources (Software or Virtual Assets)
Controlling the allowed times of downloads.
Allowing downloads only after member identity verification.
Attaching a time-limited certificate to the download URL, so it expires after a certain period.
Allowing unlimited downloads, but requiring online serial number or identity verification.
For Audio/Video Resources
Attaching a time-limited certificate to the audio-visual access URL, so it expires after a certain period.
Embedding trademarks or member account watermarks in the audiovisual content.
Using live streaming to play audio/video (downloading content as it plays, not storing the entire file in memory).
Splitting audio-visual content into chunks, each lasting about 5 seconds to the browser, makes copying extremely difficult.
Encrypting audio-visual content, with each member having a unique key for decryption, preventing sharing.
These are some of the more common anti-copying measures on the market. However, they mainly increase the difficulty of copying but can't completely stop someone who really wants to steal them. In addition, using server output instead static file access is a common solution because the server can verify identity with each access.
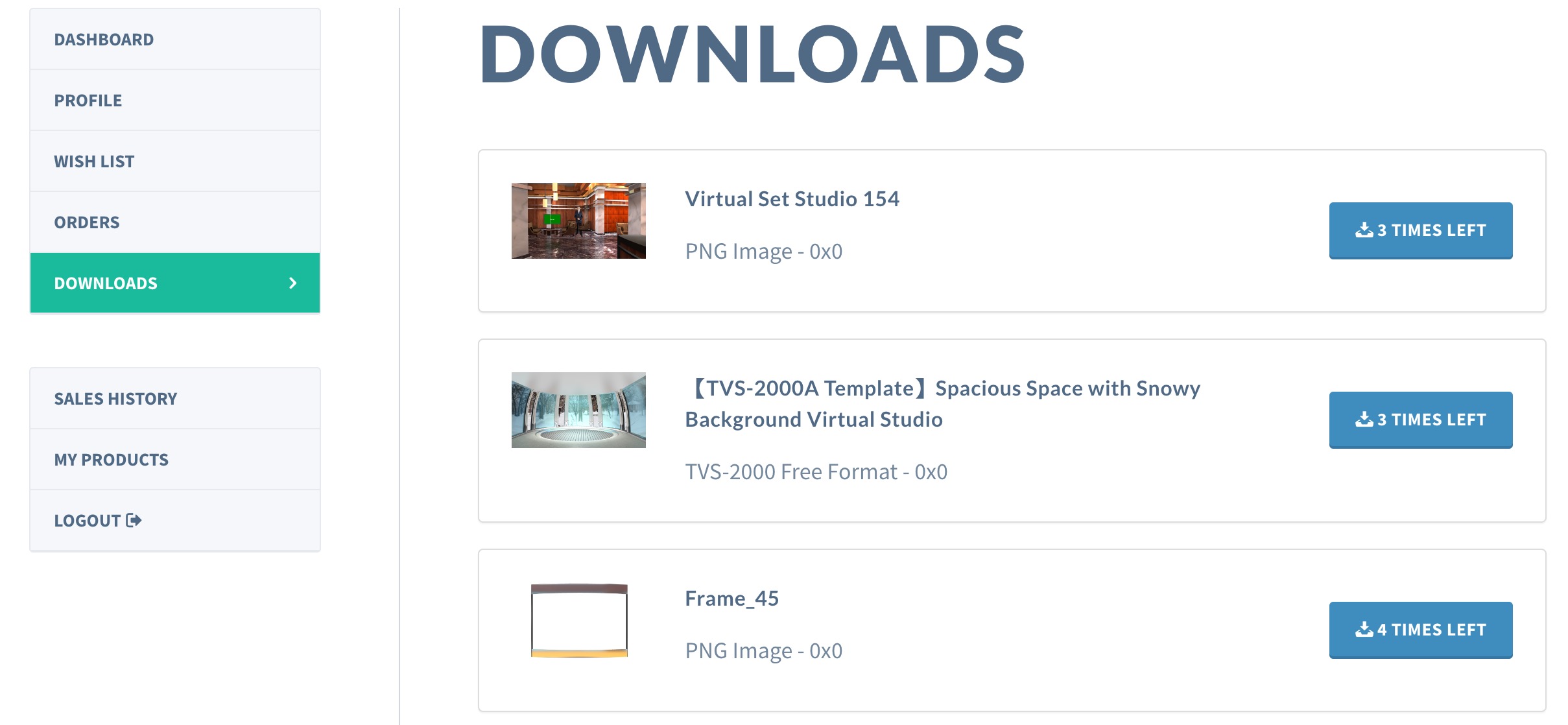
Image: Limiting times of downloads is a common DRM mechanism, The screenshot is DatavideoVirtualset website.
Common Methods of Cracking DRM
Intercepting or Stealing the Decryption Keys
Whether by hacking, reading from memory, or leaks from internal employees, owning the decryption key means directly unlocking the confidential asset and then copying it into another unencrypted version.
Exploiting Software and Hardware Vulnerabilities
Software and hardware can have vulnerabilities, especially in closed systems where flaws are not publicly known or fixed. Usually, privilege escalation is used to obtain the key.
Removing Watermarks
Rough protection methods are broken by rough methods if the stealer doesn't matter the image or audio-visual quality.
Recording or Replay Attacks
This major method of cracking DRM involves recording content during post-decryption transmission. Alternatively, all graphics and text can be screenshotted, and all audio and video can be recorded. Even if we have the hardware anti-recording protection, a smartphone can easily record the content. However, this method is not suitable for games, where the main purpose is the interactive experience.
Conclusion
Although DRM is important for protecting commercial interests, it can't 100% protect digital assets from stealing in the real world. It's mainly used to broadly verify whether purchasers have access rights. Anti-theft still requires media manipulation and legal deterrence to be effective.
Additionally, despite being easily cracked, DRM persists partly due to business and political factors. Companies selling digital resources might need to assure shareholders or original creators that the resources won't be leaked. Claiming to have DRM technology is a good way to gain trust from licensors and to some extent, take responsibility for protecting assets.

Image: For instance, "The Witcher 2" removed DRM a few days after its release due to its significant impact on performance.
As for website anti-theft, in the open culture of the Web era, all browsers can't prevent content from being copied and extracted. Thus, DRM can only control that un-purchased users can't access resources, but copying elsewhere after purchase is almost unstoppable. Creating more anti-theft features is a trade off, that may lead to additional costs and losses. For example, the developer of "The Witcher 2" released an update to remove DRM a few days after launching the game, recognizing its significant impact on performance.
However, for audio-visual resources, there are solutions. In 2017, the W3C approved a standard for Web DRM: EME (Encrypted Media Extensions), which can encrypt and decrypt audiovisual content in browsers. Although it's new and not widely used, big companies like Netflix and Spotify have already started using it. It could be a potential solution for audio-visual content theft prevention.
If you want to know more about EME, please see our next article.

![[Secure 101] What is Penetration Testing (pen testing)? How It Conducted?](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1724675801144%2Fcbdb84a4-500e-4deb-803f-a22004fbf879.png&w=3840&q=75)